Macworld
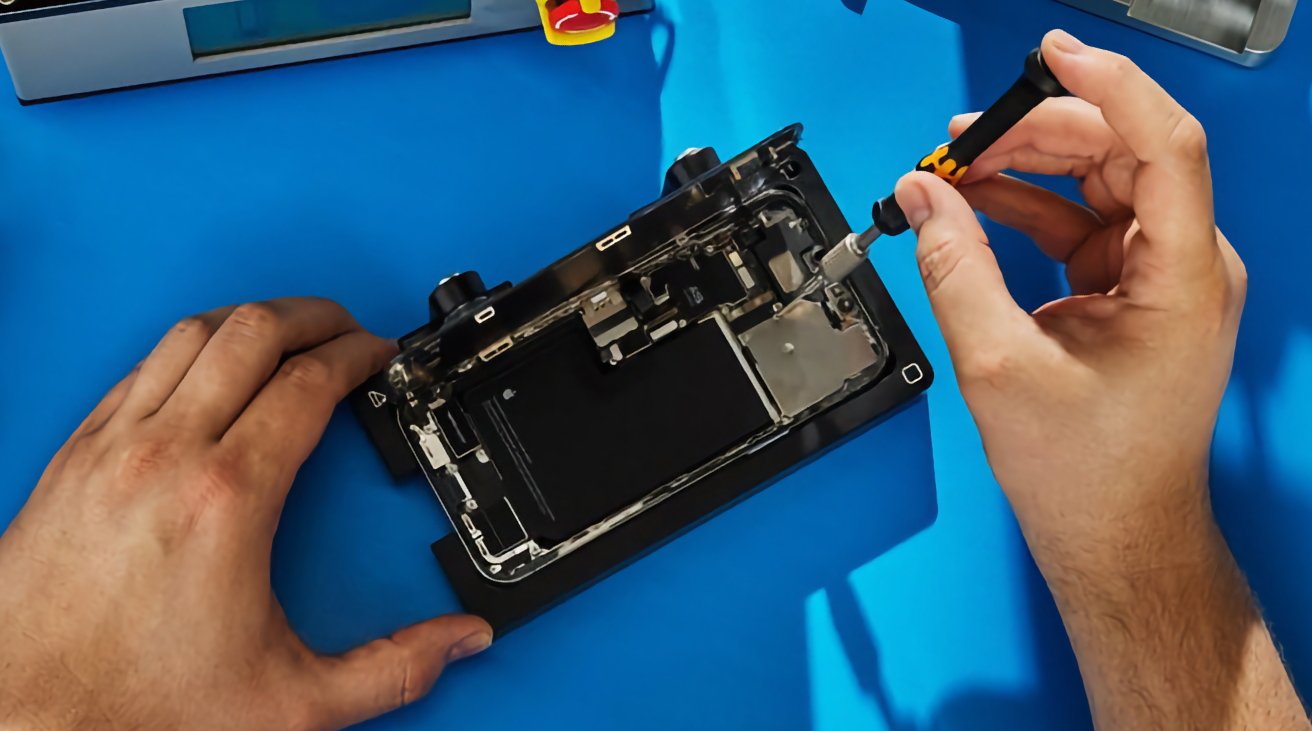
Apple’s smallest iPad was given a substantial facelift at the end of 2021. The 6th-generation iPad mini sports a complete redesign with a bigger display, Touch ID on the power button, USB C instead of Lightning, and an upgraded front camera. This represented the first major change to the design since the iPad mini was first introduced back in 2012. The mini celebrated its 10-year anniversary in 2022 without an update and no update was forthcoming in 2023 either. But a new iPad mini 7th generation is rumored to be in the works for 2024.
Update April 24: Apple announced its Let Loose iPad event for May 5, but the iPad mini is not expected to be announced.
iPad mini 7 release date: When is the new iPad mini coming out?
It’s been more than two years since the 6th generation iPad mini launched in September 2021, and, based on the dates when other iPad mini models have launched, a fall 2023 update for the iPad mini would have made sense. But now it’s looking like a new iPad mini won’t arrive until fall 2024.
Apple will hold its Let Loose event on May 7 to launch new iPads, but the iPad mini isn’t expected to be among them. Apple will reportedly release new iPad Pro and iPad Air models at the event, but the mini isn’t expected to arrive until the fall.
Way back in December 2022, respected Apple analyst Ming-Chi Kuo said the new iPad mini won’t arrive until late 2023 or early 2024. However, in November 2023, Kuo pushed that prediction back: saying the 7th-gen iPad mini won’t arrive until the second half of 2024.
iPad mini 7 price: How much will the new iPad mini cost?
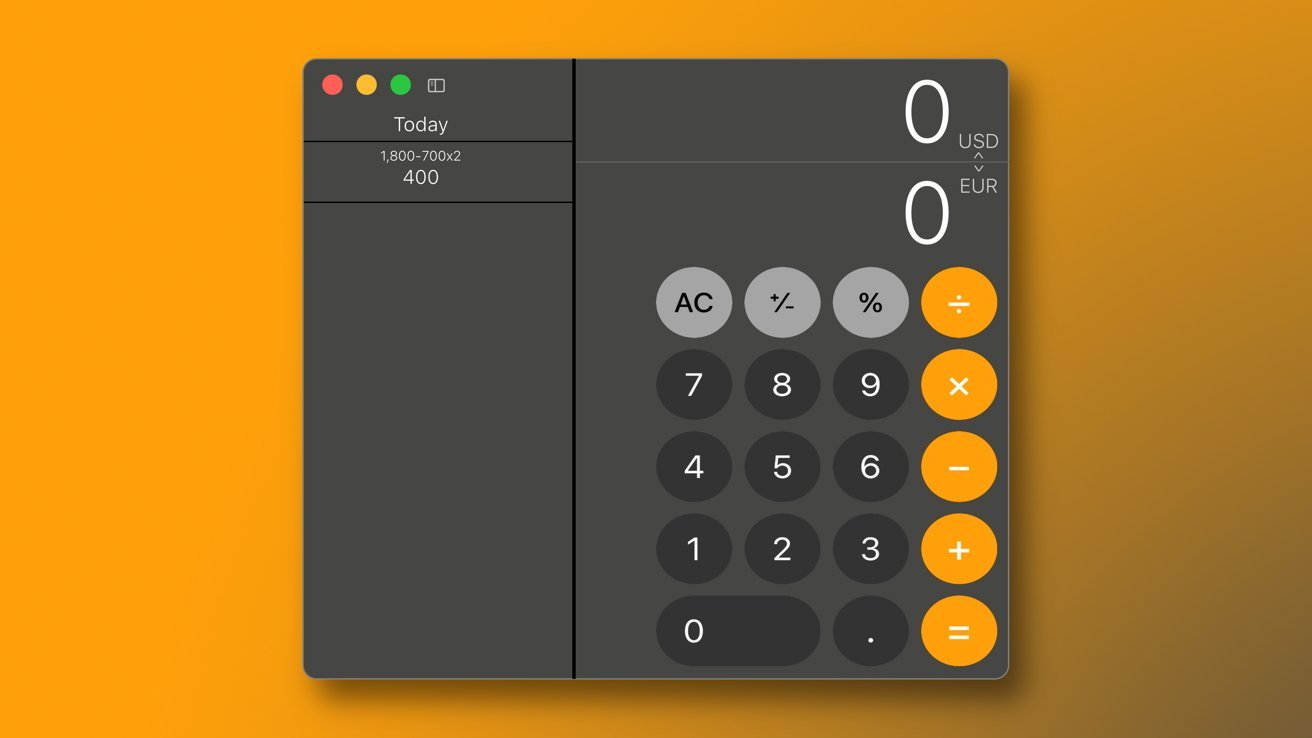
The arrival of the redesigned iPad mini 6th generation saw a $100 increase in price over the previous model to $499. Here’s how the prices of the 6th and 5th generations compared:
iPad mini 6th generation: $499/£569 (At launch was £479 in the U.K)
iPad mini 5th generation: $399/£379
That price increased even further outside the U.S. including in the U.K. where the price increased again by £90 a few months after the launch. However, it is hoped with the new generation that prices will drop in some markets. We hope that when the new models launch pricing in the U.K. will match the U.S., so $499/£499, rather than $499/£569.
iPad mini 7 specs: What new features will the iPad mini have?
There’s an expectation the new iPad mini will feature a more impressive processor than it does currently. We are also hoping for some small internal improvements.
A16 processor
The iPad mini 6 offers the A15 Bionic chip as found in the iPhone 13, mini, Pro and Max, however, this chip is down-clocked compared to the one inside the iPhone 13 series. Here’s how that chip compares to the rest of the range and what is expected for the next generation.
iPad Pro: M2. The next generation is expected to get an M3 chip.
iPad Air (5th gen): M1. The next generation is expected to get an M2 chip.
iPad mini (6th gen): A15, as found in iPhone 13 series. The next generation is expected to get A16, as found in the iPhone 14 Pro and iPhone 15.
iPad (10th gen): A14, as found in iPhone 12 series. The next generation is expected to get A16, as found in the iPhone 14 Pro and iPhone 15.
iPad (9th gen): A13, as found in iPhone 11 series. It’s unclear how (or if) Apple will update this model.
Kuo reported in December that the iPad mini’s “main selling point” would be the new processor. He didn’t specify which processor at the time, but it is now expected to be the A16 chip found in the iPhone 14 Pro and Max and the iPhone 15 and 15 Plus.
You may be looking at the iPad Air and wondering if the iPad mini might get an M1 chip like that found in the iPad Air. Perhaps it’s something Apple might consider down the line, but the rumors around the launch of the iPad Air indicated that Apple’s reason for using the M1 was actually the reduced of availability of the A16 at the time, as per this tweet from Mark Gurman.
Could also be another explanation for why the iPad Air got the M1 (supply). https://t.co/lrvuVR0QkW
— Mark Gurman (@markgurman) March 13, 2022
Increased storage
On the current iPad mini 6th generation, the base model starts off with a rather paltry 64GB of storage. For a device like an iPad, where you can store movies, TV shows, books, comics, magazines, games, and a wide range of apps, that amount can often become a problem, especially if you want to take your iPad away on holiday or use it for your commute without needing to manage the storage.
Although Apple has something of a history of giving base models low storage capacities, we think it would be a wise move to upgrade the entry-level iPad mini 7th generation to at least 128GB. File sizes are growing all the time, due to higher-quality cameras and software, so doubling the existing 64GB would be a very consumer-friendly solution.
Along these lines, there’s also the possibility that the upper limit of the storage could be increased. At the time of writing, the most storage available on the iPad mini 6th generation is 256GB. Moving up to 512GB would be the logical step, especially if the baseline storage moves to 128GB.
iPad mini 7 display: Will the iPad mini get a new screen?

The iPad mini will likely keep the same design for several generations.
![iPad mini front and back]()
The iPad mini will likely keep the same design for several generations.
IDG
![iPad mini front and back]()
The iPad mini will likely keep the same design for several generations.
IDG
IDG
It’s unlikely that the design will change, but the new iPad mini is expected to include a new display controller designed to mitigate a problem described as a “jelly scrolling issue” that reportedly makes content look laggy.
There have been reports for a while that Apple will move the display technology to OLED but this looks like it won’t happen until at least next year. Apple is said to be talking to LG, Samsung, and other companies regarding active matrix OLEDs (AMOLEDs). But, according to market research company Omdia: “Apple is continuously discussing the possibility of widely adopting OLED technology for the iPad mini and iPad Air lineup as the next phase of its strategy from 2026 onward.”
Screen size
The iPad mini screen was 7.9-inches up until the current iPad mini 6th generation launched in 2021. The iPad mini 6th generation screen is 8.3-inch thanks to the removal of the Home button.
A report from ET News suggests that an iPad mini with a larger 8.7-inch OLED display is in the works. However, this change might not happen with the 7th generation as the iPad mini with OLED screen isn’t expected until 2026.
Folding display
Apple is said to have been working on an iPad with a folding display, but it’s unlikely to come to this model. In December 2022, Ming-Chi Kuo said that reports of a folding iPad mini in development were wrong “because a foldable iPad will have a markedly higher price than an iPad mini, so such a replacement is not reasonable.”
(3/3)Additionally, Apple is currently working on a new version of the iPad mini equipped with a new processor as the main selling point, and the mass shipment is expected to start by the end of 2023 or in 1H24.
— 郭明錤 (Ming-Chi Kuo) (@mingchikuo) December 27, 2022
ProMotion screen
The screen in the 7th gen model isn’t expected to grow from the current 8.3-inch, but there may be new screen technology. A post on a South Korean forum back in November 2021 indicated Apple had ordered 8.3-inch displays from Samsung that support 120Hz maximum refresh rates. If true, the post on Clien (translated here) could mean the next mini offers the ProMotion ultra-smooth scrolling feature currently seen on the iPad Pro, iPhone 13 Pro models, and 14- & 16-inch MacBook Pro. This could address the minor issue of “jelly scrolling” that some users have complained about with the current iPad mini.
I would be surprised since it is currently an a-Si LCD which isn’t compatible with ProMotion. Only their Pro models support ProMotion as they use an Oxide LCD.
— Ross Young (@DSCCRoss) June 28, 2022
However, it’s not looking like this particular rumor is accurate. Analyst Ross Young, CEO of Display Supply Chain Consultants, doesn’t believe that Apple will be giving the iPad mini a ProMotion display yet. He indicates that doing so would require significant hardware changes. This would require a “whole new level of engineering,” according to Young.
We remain skeptical of a ProMotion upgrade as it’s one of the main differentiators between the standard and Pro devices Apple sells.
iPad mini design: What will the new iPad mini look like?
It’s been surprisingly quiet on the rumor front, which probably means the iPad mini 7 design will be largely the same as the 6th-gen model. Here’s what we’ve managed to uncover.
One of the most obvious changes to the iPad mini 6th generation was the new palette of colors that Apple made available.
While you can currently select between space gray, pink, purple, and starlight, there are several interesting hues available on the iPad Air when it received its new look in fall 2021, including silver, rose gold, green, and sky blue. It would therefore seem reasonable to assume that some of these make it to the mini. Plus now that the iPad 10th generation brought a bold selection of colors, the iPad mini may get a completely new palette. However, the iPhone 15 introduced an extremely light palette of colors so it’s unclear which direction Apple will go.
We’ll update this article as more details become available, but until then, be sure to read our iPad buying guide to see which models we’d recommend if you want to buy one of Apple’s tablets today. And check our roundup of the best iPad mini deals for the latest bargains on the current range.
iPad
]]>

 Apple Watch Ultra 2
Apple Watch Ultra 2


 Steve Jobs holding the original iPhone during his keynote address at MacWorld Conference & Expo in 2007. (Photo: Paul Sakuma/Associated Press)
Steve Jobs holding the original iPhone during his keynote address at MacWorld Conference & Expo in 2007. (Photo: Paul Sakuma/Associated Press)



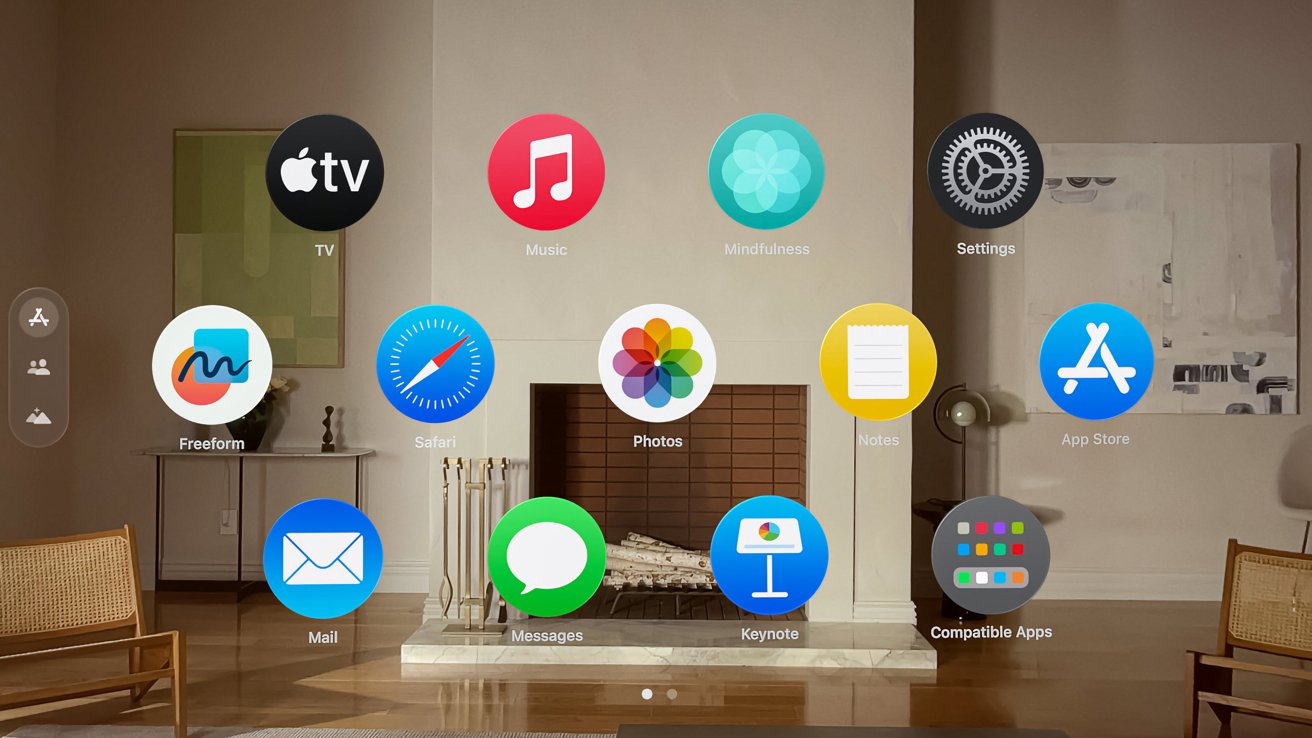
 Apple Vision Pro features a pair of advanced, custom micro‑OLED displays deliver more pixels than a 4K TV to each eye — for stunning clarity.
Apple Vision Pro features a pair of advanced, custom micro‑OLED displays deliver more pixels than a 4K TV to each eye — for stunning clarity.

 The limited series drama “The Big Cigar,” starring André Holland, is set to premiere globally on May 17th on Apple TV+.
The limited series drama “The Big Cigar,” starring André Holland, is set to premiere globally on May 17th on Apple TV+.




 Apple’s current Mac Studio front (top image) and rear
Apple’s current Mac Studio front (top image) and rear




 Apple’s new drama series “Neuromancer” will be based on William Gibson’s science fiction novel of the same name.
Apple’s new drama series “Neuromancer” will be based on William Gibson’s science fiction novel of the same name.

 The cheapest M2 Mac mini price is currently available at Amazon, with the standard model featuring an 8-core CPU and 10-core GPU discounted to $499.99. The savings are in the form of a $49.01 on-page coupon that stacks with a $50 instant rebate already in place.Buy for $499.99If you’re looking for the best deal on upgraded models, our M2 Mac mini Price Guide is home to exclusive coupon savings on every configuration — with discounts of up to $250 off using promo code APINSIDER during Step 4 of checkout at Apple Authorized Reseller Adorama. Continue Reading on AppleInsider
]]>
The cheapest M2 Mac mini price is currently available at Amazon, with the standard model featuring an 8-core CPU and 10-core GPU discounted to $499.99. The savings are in the form of a $49.01 on-page coupon that stacks with a $50 instant rebate already in place.Buy for $499.99If you’re looking for the best deal on upgraded models, our M2 Mac mini Price Guide is home to exclusive coupon savings on every configuration — with discounts of up to $250 off using promo code APINSIDER during Step 4 of checkout at Apple Authorized Reseller Adorama. Continue Reading on AppleInsider
]]>


 Apple Arcade offers unlimited accessto 200+ incredibly fun games, with more added all the time. Play across your Apple devices with no ads, no interruptions, and no in-app purchases.
Apple Arcade offers unlimited accessto 200+ incredibly fun games, with more added all the time. Play across your Apple devices with no ads, no interruptions, and no in-app purchases.





 Led by small business owners, the sessions will highlight how these organizations have used Apple products and resources to build their businesses, reach customers in new ways, and push their organizations forward.
Led by small business owners, the sessions will highlight how these organizations have used Apple products and resources to build their businesses, reach customers in new ways, and push their organizations forward.




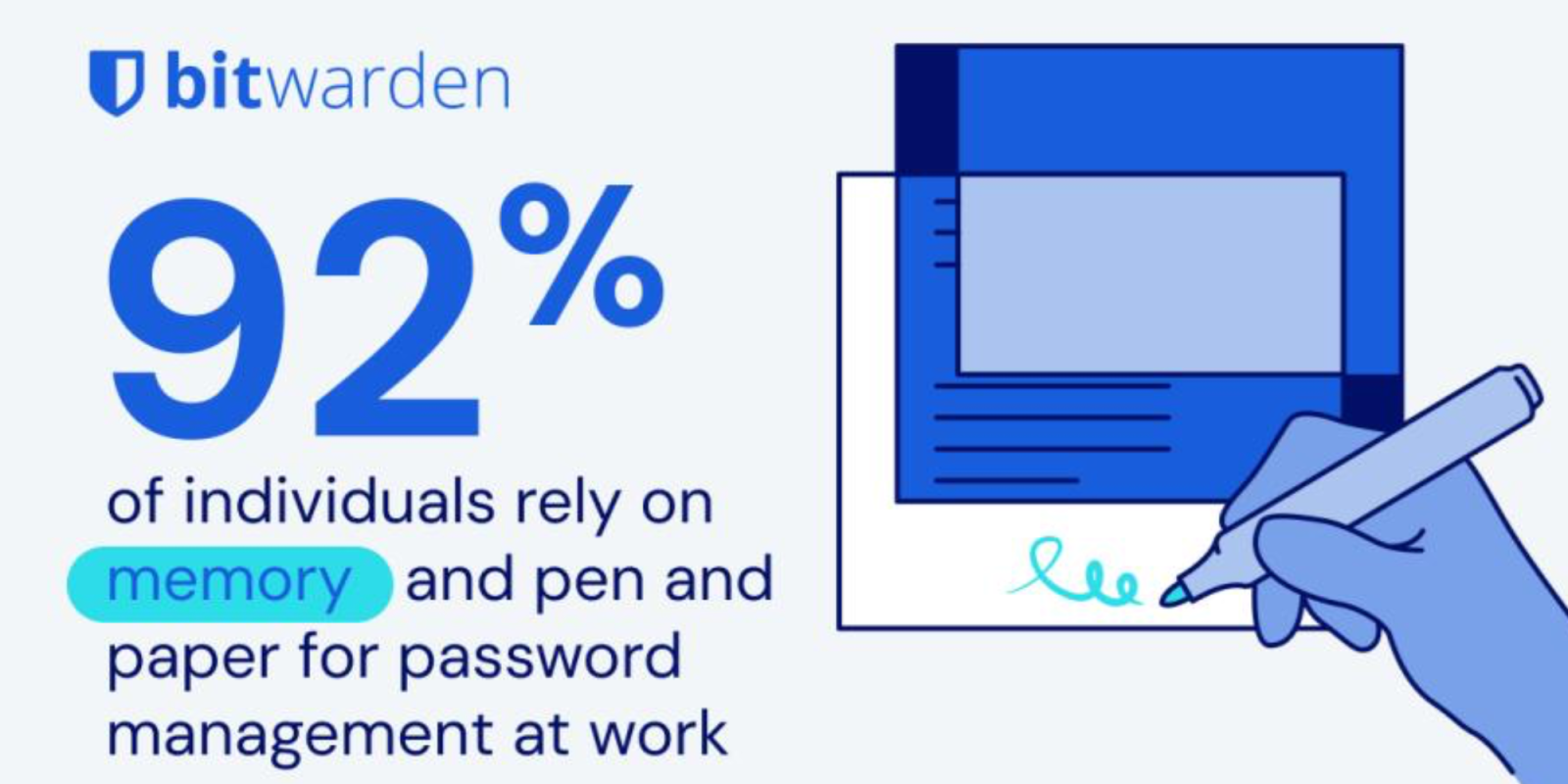



 Brute force cracking of passwords takes longer now than in the past, but the good news is not a cause for celebration, according to the latest annual audit of password cracking times released Tuesday by Hive Systems. The post Brute Force Password Cracking Takes Longer, But Celebration May Be Premature appeared first on TechNewsWorld.
]]>
Brute force cracking of passwords takes longer now than in the past, but the good news is not a cause for celebration, according to the latest annual audit of password cracking times released Tuesday by Hive Systems. The post Brute Force Password Cracking Takes Longer, But Celebration May Be Premature appeared first on TechNewsWorld.
]]>













 Apple CEO Tim Cook
Apple CEO Tim Cook


 Continue Reading on AppleInsider
]]>
Continue Reading on AppleInsider
]]>



 It’s already known that TSMC has been developing 3 nanometer processors, and believed that Apple has bought out its entire production capacity for it. The presumption was that Apple would use the process for latest versions of its A-series iPhone chips, and M-series Mac ones.Now, however, a leaker named “Phone Chip Expert” on Chinese social media site Weibo, claims that Apple is designing a specific, bespoke artificial intelligence processor. As first spotted by MacRumors, the leaker says it will go into mass production in the second half of 2025.If correct, this suggests that Apple is not exclusively focusing on AI being run locally on device. It’s been presumed that Apple prefers AI running on the iPhone because of privacy, but so far AI has required greater processing capacity, and storage, than is always available on device. Rumor Score: 🤔 Possible Continue Reading on AppleInsider | Discuss on our Forums
]]>
It’s already known that TSMC has been developing 3 nanometer processors, and believed that Apple has bought out its entire production capacity for it. The presumption was that Apple would use the process for latest versions of its A-series iPhone chips, and M-series Mac ones.Now, however, a leaker named “Phone Chip Expert” on Chinese social media site Weibo, claims that Apple is designing a specific, bespoke artificial intelligence processor. As first spotted by MacRumors, the leaker says it will go into mass production in the second half of 2025.If correct, this suggests that Apple is not exclusively focusing on AI being run locally on device. It’s been presumed that Apple prefers AI running on the iPhone because of privacy, but so far AI has required greater processing capacity, and storage, than is always available on device. Rumor Score: 🤔 Possible Continue Reading on AppleInsider | Discuss on our Forums
]]>